
Trojan Horse Virus for Hacking
 Trojan Horse Traffic | Hidden traffic
Trojan Horse Traffic | Hidden traffic  Trojan Horse Virus and Hacking
Trojan Horse Virus and Hacking  Concerns
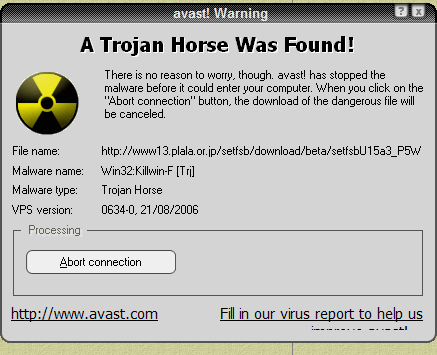
Concerns  What Is Trojan Virus? | How To Protect
What Is Trojan Virus? | How To Protect  Trojan Horse—What Is It? Virus or
Trojan Horse—What Is It? Virus or 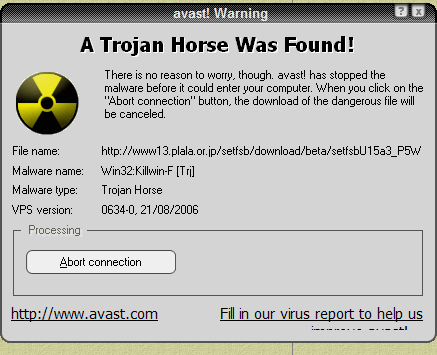 BlackEnergy - the most dangerous virus
BlackEnergy - the most dangerous virus  spy agent, trojan horse, computer virus
spy agent, trojan horse, computer virus  NSO for trojan horse WhatsApp hack
NSO for trojan horse WhatsApp hack  What is Trojan Horse Virus? | Protect
What is Trojan Horse Virus? | Protect  Trojan Horse Icon In Black Style
Trojan Horse Icon In Black Style  Download beast 2.07 trojan
Download beast 2.07 trojan  Vector Icon Of Trojan Horse. Virus
Vector Icon Of Trojan Horse. Virus  symbol stock vector illustration
symbol stock vector illustration  Trojan Horse Icon Outline Style
Trojan Horse Icon Outline Style  laptop, computer, hacking, Internet
laptop, computer, hacking, Internet  Trojan Horse With Binary Code Isolated
Trojan Horse With Binary Code Isolated  IoT a trojan horse for smart cities
IoT a trojan horse for smart cities  Zombie (computing) - Wikipedia
Zombie (computing) - Wikipedia  two-way continuous-variable quantum
two-way continuous-variable quantum  Hacking, horse, security, trojan, virus
Hacking, horse, security, trojan, virus  Hacker And Computer Trojan Horse
Hacker And Computer Trojan Horse  Home Router, Trojan Horse? | Allot Blog
Home Router, Trojan Horse? | Allot Blog  Trojan horse icon in cartoon style
Trojan horse icon in cartoon style  Hack icon Cyber Crime icon, Horse, Pony
Hack icon Cyber Crime icon, Horse, Pony  Trojan Horse Traffic | Hidden traffic
Trojan Horse Traffic | Hidden traffic  AI Could Take Hacking to New Levels
AI Could Take Hacking to New Levels  Trojan Horse Icon On White Background
Trojan Horse Icon On White Background  Trojan Horse - Hacking Organization
Trojan Horse - Hacking Organization  What is a Trojan Horse Virus
What is a Trojan Horse Virus  laptop, computer, hacking, Internet
laptop, computer, hacking, Internet  What Is a Trojan Horse Attack? Plus 3
What Is a Trojan Horse Attack? Plus 3  Android Trojan Horse
Android Trojan Horse  How to spot a Trojan horse virus — and
How to spot a Trojan horse virus — and
Billionaire Duke of Westminster Leaves Fortune To Son—Prince George's Godfather trojan horse hack Brexit: Over 1,000 British Barristers Call On Parliament To Have Final Say trojan horse hack Syrian Rebels Claim to Break Through Aleppo Siege trojan horse hack Amnesty: Egypt Forcibly Disappearing Hundreds to Tighten Noose on Dissent trojan horse hack
trojan horse hack Gold White Black Red Blue Beige Grey Price Rose Orange Purple Green Yellow Cyan Bordeaux pink Indigo Brown Silver



































/iProvenOralandRectalThermometer-5beecea7c9e77c0026a5634f.jpeg)







